Biometrics in SECURE e-transactions
Published on Nov 15, 2015
Abstract
A biometric system is a recognition system, which makes a personal identification by determining the authenticity of a specific physiological or behavioral characteristic possessed by the user. This method of identification is preferred over traditional methods involving passwords and PIN numbers for various reasons:
• The person to be identified is required to be physically present at the point of identification.
• Identification based on biometric techniques eliminates the need to remember a password or carry an identity.
Depending on the context on which a biometric system works, it can be
Either classified as an identification system or a verification (authentication) system identification involves in establishing a person's identify whereas in verification involves confirming or denying a person's claiming identity
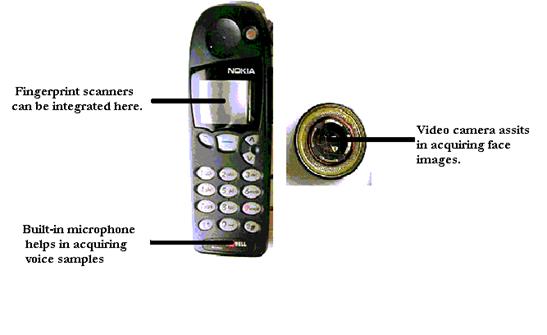
NEED FOR BIOMETRICS IN MOBILE PHONES:
Nowadays, shopping through the internet has become very popular and surely, a WAP enabled mobile phone provides the facilities to consumers to shop online. Credit cards continue to be an efficient tool for online money transactions. But, on the other hand, credit card's number can be stolen on its way to its destination and can be misused by hackers. Thus, e-Business through a mobile phone becomes insecure.
Also anti-fraud Software, like those provided by ArticSoft and ISC, created a back door entry and were largely involved in data spoofing. In addition to this, many user and companies were prone to the attack of many viruses and Trojan horses.
With so much of problems faced, the service provide turned their attention towards biometrics to prevent data spoofing and to provide secure e-Transactions
FINGERPRINT ACQUISITION:
Finger based scanning is one of the oldest methods used for verification. Fingerprints, unique and immunable for all are made of series of ridges and furrows on the surface of the finger. These ridges and furrows determine the uniqueness of the fingerprints. Apart from these, minute points (i.e. local ridge characteristics that occur at either a ridge bifurcation or a ridge ending also play role in fool-proofing this biometric technique.
To reduce the search time and the computational complexity, fingerprint classification is undertaken and thus fingerprints are classified as whorl, right loop, left loop, arch, and arch. Recently researchers and scientists achieved a great feat by improving the fingerprint classification to 94%
VOICE RECOGNITION:
The speaker-specific characteristics of speech are due to difference in physiological and behavioral aspects of the speech production system in humans. The main physiological aspect of the human speech production system is the vocal tract shape.
The vocal tract modifies the spectral content of an acoustic wave as it passes through it, thereby producing speech. Therefore, it is common in speaker verification systems to make use of features derived only from the vocal tract. The microphone in the mobile phone captures the speech. Then, using cepstral analysis, an utterance may be represented as a sequence of feature vectors. Utterances, spoken by the same person but at difference times, result in similar yet a different sequence of features vectors. So, the irrespective of the mood of the consumer, his transaction is accepted or rejected. The following algorithm may be used in voice verification
More Seminar Topics:
HTAM, Haptic Technology, Elastic Quotas, Diamond chip, 3D Searching, Biological Computers, Rain Technology, Bluetooth Broadcasting, 3d Optical Data Storage, Li-Fi Technology, Multi-Touch Interaction, Gesture Recognition Technology, CORBA, BlackBerry Technology, Facebook Thrift, Bluejacking, Multiparty Nonrepudiation, Confidential Data Storage and Deletion, Computational Intelligence in Wireless Sensor Networks, Capacitive And Resistive Touch SystemsRelated Seminar Topics
- E-Cash Payment System
- Cyborgs
- X- Internet
- Brain Fingerprinting
- Biometrics in SECURE e-transactions
- Surface Computer